Hi Everyone! Do you like tinkering with websites? Like for fun trying to make your own website? So, for those of you who are already bored using the PHP programming language, you can move on to Node.js. Want to know what is Node.js and its advantages? Please read the advantages of Node.js in Website Development . As a substitute for the PHP programming language, of course Node.js also has various web frameworks. In PHP, you can find frameworks like Codeigniter, Laravel and Yii. In Node.js you can also find web frameworks such as Express.js, Sails.js and Kraken.js. So, in this guide, KincaiHosting will explain how to install Express.js on Hosting . Want to know? Let's follow step by step.
Also Read: Tips for Choosing the Best Hosting
What is Express.js?
Before getting into how to install, you should first get acquainted with Express.js. What is Express.js? Quoted from the official website, Express.js is a type of Node.js-based web framework. In express.js, you can find several modules, helpers and libraries like a normal PHP framework.
Why Should I Use Express.js?
There are several reasons why you should look to Express.js as the framework of choice. 1. Fast
and Flexible 2. Many
features for website development
3. There is middleware support 4. Support
HTTP verbs such as POST, GET, PUT and so on
5. The routing and helper used are very easy and structured
6. The documentation is complete and easy to understand
Preparation phase
There are several things you need to prepare before following How to Install Express.js, namely.
First , you must know how to access the server via SSH. This will come in handy later during the installation. So for those of you who don't know, please read How to Access SSH via Terminal or PuTTy . Or for those of you who don't know what SSH is, please read What is SSH Server .
Second , because the installation process uses a lot of Linux commands, you should first get acquainted with various Linux commands. For those of you who don't know, you can read 10 Linux Commands You Need to Know .
Third , make sure you have installed Node.js. For guidance, you can check onHow to Install Node.js on Hosting
After the three preparations have been made, then you are ready to install Express.js :))
How to Install Express.js on Hosting
The way to install Express.js on Hosting is as follows.
1. Determine the Install Location
The first thing you have to think about is the location where Express.js will be installed. Is it in the main domain? Is it on a subdomain? If in the main domain, please install it in public_html. If on a subdomain, please install Express.js in its folder.
For example:
Main domain: websitesaya.com
Subdomain: express.websitesaya.com
To create a subdomain, please follow the guide on How to Create a Subdomain on Hosting .
2. Create a NodeJS App
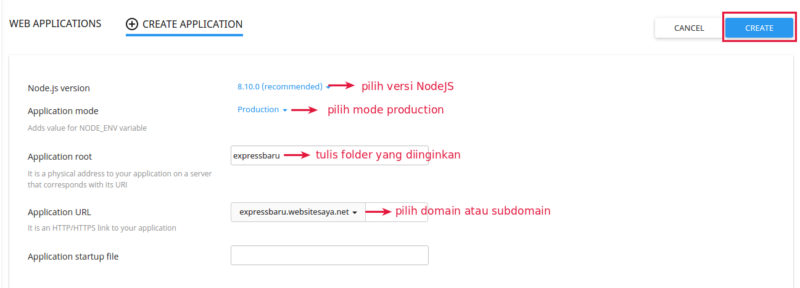
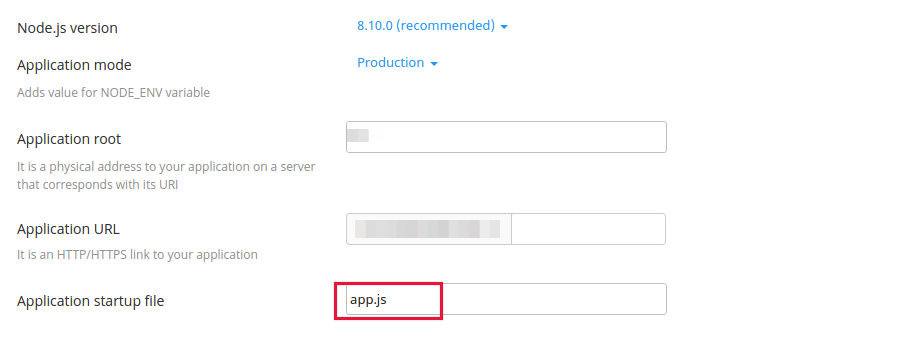
Because Express.js is a Node.js based web framework, you must first create a NodeJS App in cPanel. Please login cPanel and select menu Setup Nodejs App. Please make it according to the NodeJS Setting Guide .
Then select the version of NodeJS to use. We recommend using NodeJS version 8.10.0 as it is stable. In Application mode, please select mode Production. On Application root, you can create a folder for the installation. After that click Create.
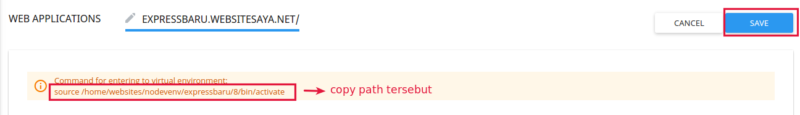
Wait a moment until it appears as shown. Make sure you have copied / copied the path in Command for entering to virtual environment: . Don't forget to remember the name of the folder you created! This path will be used for Express.js installation on Hosting.
3. SSH access via Terminal or PuTTy
Then all you have to do is access the server via SSH using the Terminal or PuTTy Software. For you Linux or Mac users, you can use the terminal. For you Windows users, you can use PuTTy Software. If you don't know how, please read the SSH Access Guide . Write
ssh username @ controlpanelURL –p 64000
Remember, SSH access can only be done on Super Hosting Packages and above !
4. Enter the Node Environment
The Express.js installation must be done in the Node.js environment that was created earlier. After successfully entering hosting via SSH, you can immediately enter the node environment. As for the method, namely, the path that you copied earlier, please paste it in the terminal. For example,
source / home / websites / nodevenv / expressbaru / 8 / bin / activate
After pasting and entering, the display will change. The folder will be moved to the environment node based on the folder that was created earlier.
![]()
5. Configure NPM
Please enter the folder that was created earlier. Because Express.js is based on NodeJS, this time the package manager used is npm. Well, please write the following command,
NODE_ENV = production npm install
Then write it down
npm init
This command is used to create a package.json file. Wait a moment until the process is complete.
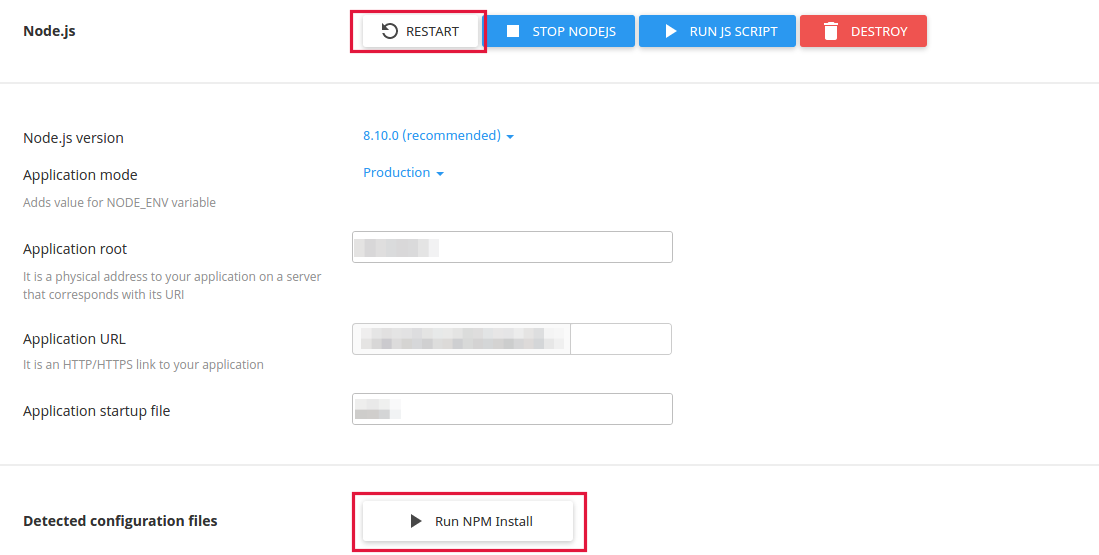
After that, please open the page Setup NodeJS Appon cPanel Hosting again. Please click Run NPM Install. Wait a moment then click Save. After that click Restart.
6. Install Express.js on Hosting
Now, go back to terminal / console mode. Now to install Express.js, please write the following command,
npm install express
Wait a moment for the installation process to complete. If so, you can get a folder node_modulesthat contains several folders, one of which is the express folder.
7. Run the ExpressJS file
So, to find out whether the Express.js install process was successful, you have to create a Node.js based file. You can use the nano or vim command.
vim app.js
Then fill in the following code:
|
var express = require('express'); var app = express(); // Routes app.get('/', function(req, res) { res.send('Hello World!!!!!!!!!!!!!!!!!!!!'); }); // Listen var port = process.env.PORT || 3000; app.listen(port); console.log('Listening on localhost:'+ port); |
Note: For those of you who are not familiar with using vim, please copy the script above. Then write vim index.js. When a blank screen appears, please right click select paste. After that, to save the script, please press "Esc" on the keyboard. Then write: wq and enter.
8. Express.js Install Process Successful!
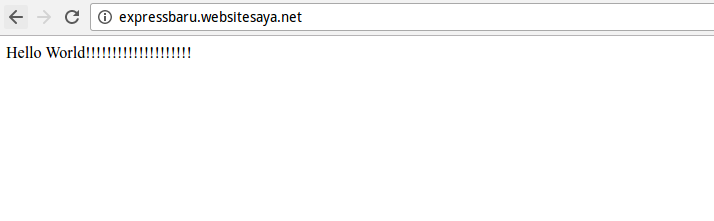
Okay, try now to open a web browser then write according to your domain name. If using a subdomain, make sure to write the subdomain as well. And look what happened! If successful, the app.js file will run successfully.
Make sure the Application startup file, you write according to the ExpressJS file you want to run. In this case, please write app.js.
Oh yes, you can also check Express.js service through the terminal. Please write the following command,
Closing
So, how to install Express.js is very easy, right? Indeed, for those who are not used to using Linux terminal commands, it will be quite confusing. But if you follow the step by step method above, we make sure you will find it easier to install. Don't hesitate to contact the KincaiHosting Support Team if you are having trouble! Interested in Quality Cheap Hosting ? Just check KincaiHosting Hosting !
Also Read: How to Make Your Own Online Store
